
For most potential buyers looking at HashiCorp Vault (IBM Vault) alternatives, the core question is does paying the operational costs of running Vault make sense, or is a more cost-effective secrets management tool like SplitSecure a better fit.
If Hashicorp Vault’s operational requirements make you hesitate, then Splitsecure is probably a better alternative. Learn more.
Hashicorp’s/IBM's offering is a very powerful secrets management engine. It can handle dynamic secrets, encryption-as-a-service, PKI, database credential rotation, and more. For engineering-heavy organizations with dedicated platform teams, that flexibility (and possibilities for configuration) is a strength.
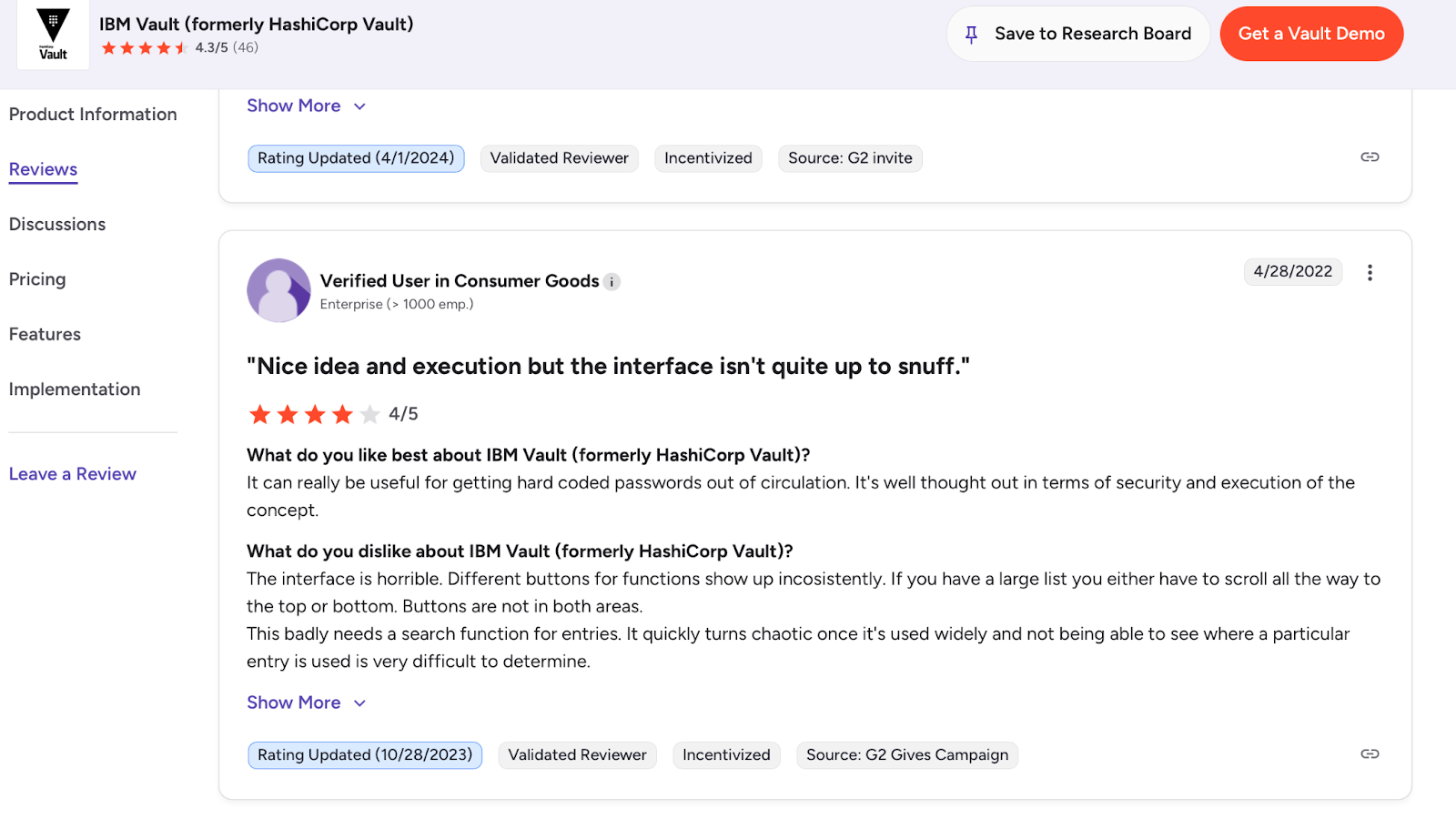
But HashiCorp Vault (IBM Vault)’s core technology and functionality were designed by engineers for engineers. The consequences of that show up in production for end users. If your team has higher priority work than managing secrets infrastructure and can’t dedicate the resources, you are better off choosing an alternative.
Also, since IBM's $6.4 billion acquisition of HashiCorp closed in early 2025 and Vault became part of the Security QRadar Suite, it’s worth raising questions about the product's long-term direction, licensing changes, and support responsiveness, given IBM’s historical record of supporting products post-acquisition.
Note: In this comparison, we call Hashicorp Vault “HashiCorp Vault (IBM Vault)” or “HashiCorp Vault (IBM)” because both naming conventions are currently used by IBM and third parties, as well as “IBM HCP Vault.”
In this article, we draw on HashiCorp Vault’s (IBM Vault) own documentation and customer reviews on G2, Gartner Peer Insights, Reddit, and PeerSpot to give an honest comparison of when Vault makes sense and when SplitSecure is a better alternative for secrets management.
Vault has been a default secrets management choice in engineering-heavy enterprise organizations for years. Several factors are driving teams to evaluate alternatives in 2026.
Running Vault in production means running infrastructure. You'll need a storage backend (Consul, Raft, or a cloud provider's storage), ongoing cluster health management, a process for unsealing after restarts, and engineers who understand Vault's internals well enough to troubleshoot issues under pressure.
For organizations that already have a strong platform engineering team, this is manageable.
However, the reality of living with Vault is likely more than most organizations can handle. Almost every PeerSpot review of Vault mentions complexity, instability, and a lack of self-service onboarding as major downsides.
As one Reddit user responded to a r/devops question about whether to use Vault:
“You have a problem, You opt to use Vault, You now have more problems.”
IBM closed its $6.4 billion acquisition of HashiCorp in early 2025. For anyone planning a multi-year deployment, this must raise questions about support responsiveness, feature direction, and pricing trajectory, which makes evaluating a Vault alternative a reasonable hedge.
Right now, we are reading forum posts from users complaining about IBM audit requirements and other potential changes to the terms of service.
SplitSecure takes a fundamentally different approach to secrets management than HashiCorp Vault.
Instead of storing complete credentials in a centralized vault protected by unseal keys and root tokens, SplitSecure uses team-based access control to split secrets across a group of devices. No single device ever persists the protected credentials.
This is important because inside every organization, there are secrets protected by other secrets. Vault itself is a textbook example in that the credentials it manages are protected by unseal keys, which are protected by the operators holding them, which are, in turn, protected by their own credentials. Many organizations opt for “auto-unseal,” which introduces a new layer of risk via the services used for unseal operations.
The same is true for other solutions like CyberArk, where no matter how many layers you add, there is always a "last secret" protecting the entire system. SplitSecure solves this "last secret" problem.
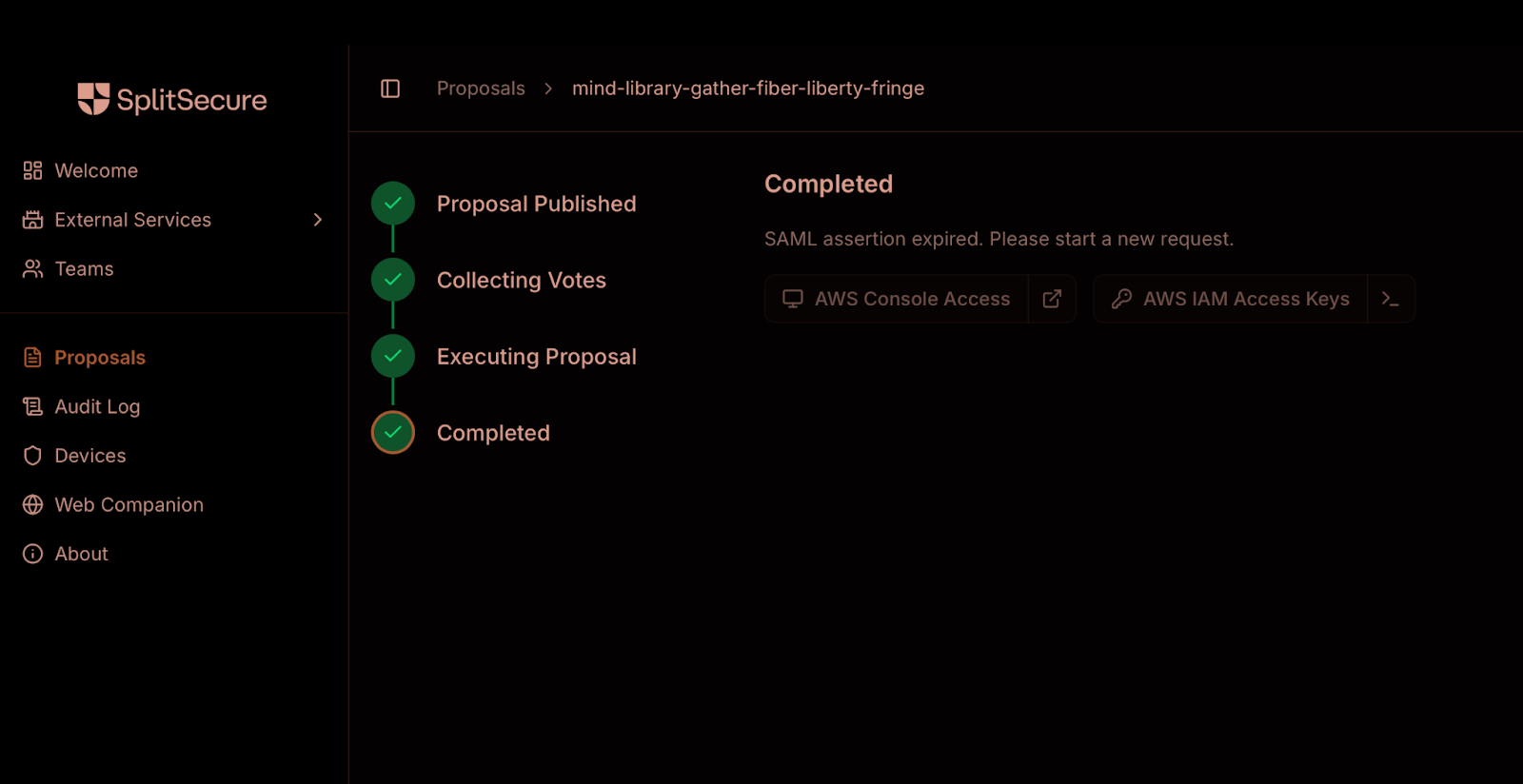
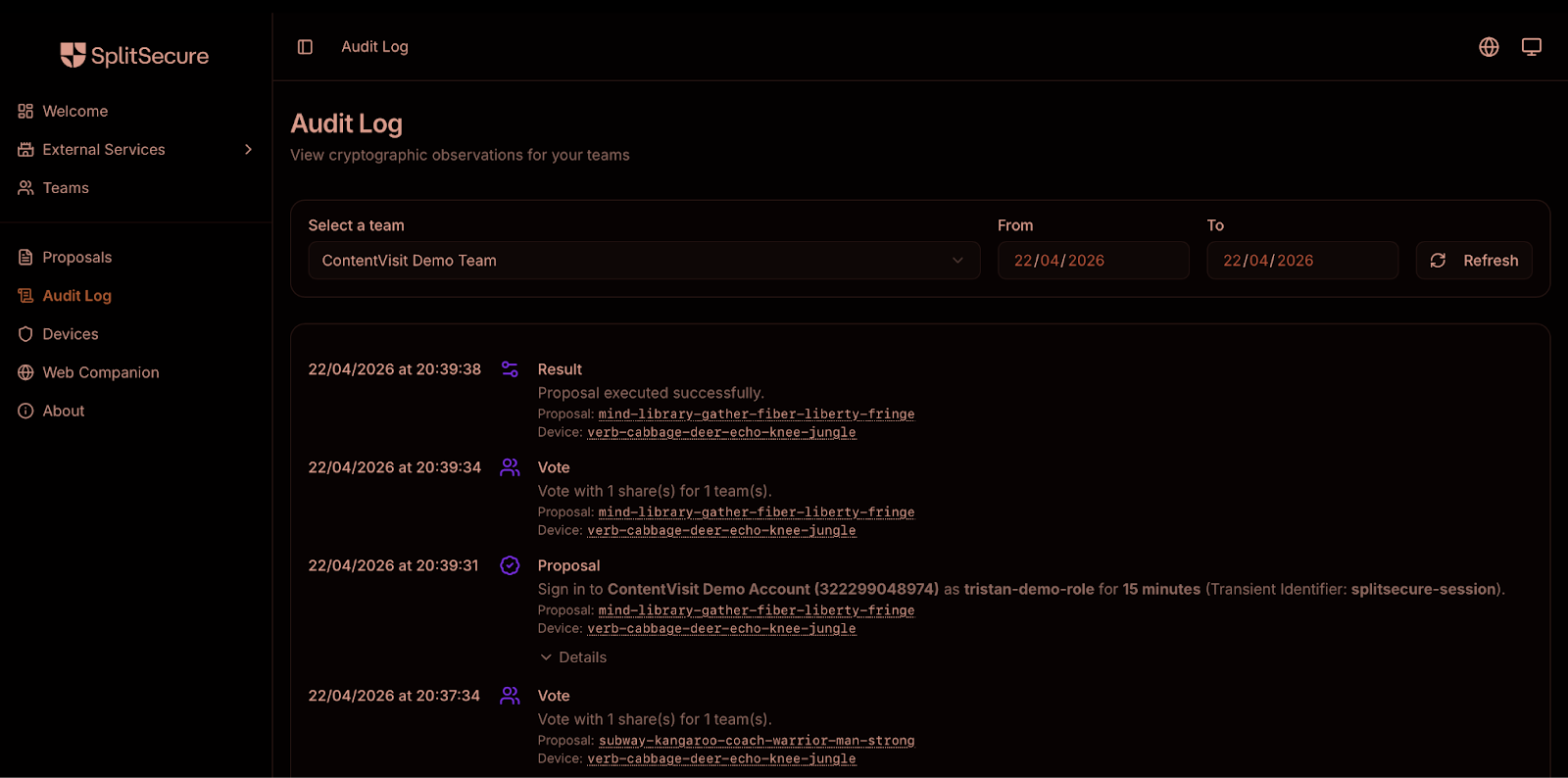
When an employee or system wants to access a credential protected by SplitSecure, the request is submitted to a "team" of devices. For example, a credential might be protected by a team consisting of an engineer's iPhone, their laptop, and the enterprise's Okta deployment.
When these entities collectively confirm that the access request complies with company policy, access is automatically granted and occurs invisibly in the background. Attackers would need to compromise multiple devices simultaneously (a 'threshold') to extract protected information.
Like Vault, SplitSecure provides separation of duties and audit trails. Unlike Vault, these properties are mathematical rather than policy-based. You cannot use SplitSecure’s system without creating an audit record. And separation of duties is not a configuration setting you define with ACLs and Sentinel policies, but a cryptographic property of how the architecture works.
SplitSecure also doesn’t require you to manage cluster infrastructure or backend storage (though it can be self-hosted if you wish). Any IT person can have SplitSecure up and running in under an hour without specialist expertise.
And if SplitSecure ceased operations tomorrow, your deployments would continue to function, whereas previous breaches of HashiCorp's infrastructure (such as the 2021 incident) have caused real disruption for customers.
Below, we break down four situations a team evaluating Vault is likely to encounter.
If your primary use cases are dynamic database credentials, PKI, encryption-as-a-service, and CI/CD pipeline secrets, and you have engineers comfortable running Vault infrastructure, it remains the strongest tool for the job.
Vault's learning curve is steep, and running it in production requires ongoing engineering attention. If your team doesn’t have engineers who can troubleshoot Vault cluster issues, manage unseal keys, and maintain storage backends, the operational reality won’t match the product's capabilities. In this case, SplitSecure is the better fit. SplitSecure deploys in under an hour and requires no infrastructure to maintain.
SplitSecure is a far easier way to deploy regulatory-compliant privileged access and secrets management than Vault. SplitSecure lets financial institutions assign access as needed without ever moving or sharing cryptographic material. It also logs how secrets are used, including every time a secret is requested.
SplitSecure can protect your highest-sensitivity credentials, things like admin passwords, signing keys, and root secrets, with cryptographic separation of duties, while Vault continues to handle dynamic secrets and engineering infrastructure.
If Vault's operational overhead, pricing trajectory, or compliance gaps are driving your evaluation, SplitSecure offers a fundamentally different approach.
No clusters to manage and unseal keys to protect.
Simple to use and deploy, with cryptographic separation of duties that cannot be overridden. Running in under an hour.
Learn more about how SplitSecure works, or contact us if you’d like to talk to a real person.
It depends on your use case. If you need dynamic database credentials, PKI, and encryption-as-a-service for engineering infrastructure, Vault is purpose-built for that, and SplitSecure isn’t a replacement. If your primary need is protecting privileged credentials with separation of duties and compliance-ready audit trails, SplitSecure can replace Vault for that use case entirely.
Larger teams are often best served by running both: Vault for engineering secrets and SplitSecure for the highest-sensitivity credentials that need cryptographic separation of duties.
The opposite. SplitSecure deploys in under an hour with no infrastructure required. Vault requires cluster setup, storage backend configuration, unsealing procedures, and ongoing maintenance. Vault's learning curve is consistently cited in user reviews as a significant barrier, particularly for teams without dedicated platform engineering resources.
SplitSecure meets separation of duties, audit trail, and third-party risk requirements through its architecture rather than through configuration. Vault's Enterprise tier provides policy enforcement (Sentinel), namespaces, and HSM support, but these are configuration-dependent. SplitSecure provides compliance properties as a structural default. For FFIEC, NYDFS Part 500, DORA, and OCC requirements, this architectural approach means compliance does not degrade when configurations drift or policies are overridden.
Our Blog